Data Security
Data Security focuses on protecting sensitive enterprise data across SAP production and non production landscapes. This category covers practical approaches to SAP data security including access control, data masking and scrambling, real time enforcement, governance, audit evidence, and regulatory compliance. Topics support organisations running SAP ECC and S/4HANA that need to reduce exposure, prevent misuse of copied data, and demonstrate enforceable security controls in day to day operations.
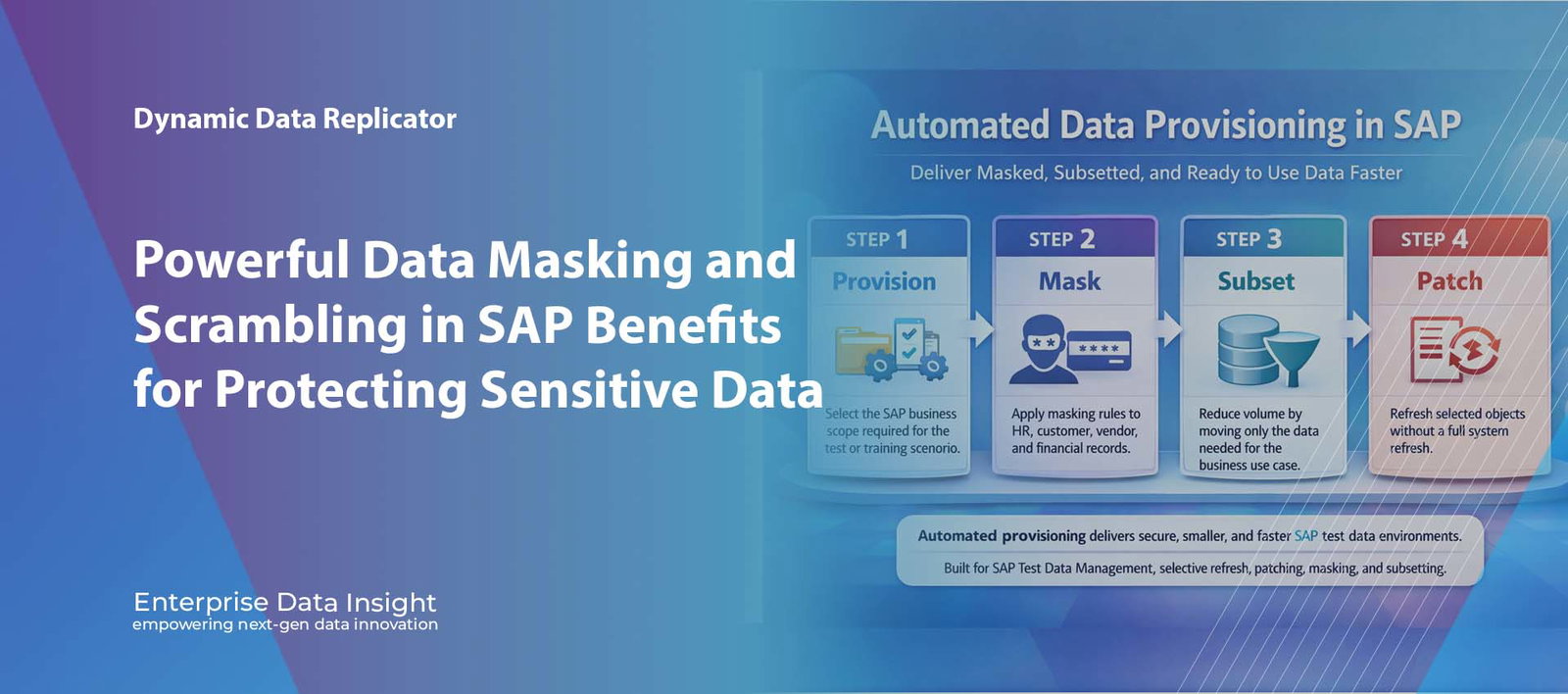
Automated Data Provisioning | Data Masking | Data Subsetting Automated Data Provisioning in SAP: How Masking, Subsetting, and Patching Deliver Faster and Safer Test Data Automated Data Provisioning in SAP is changing how organisations prepare non production systems for testing, training, development, and project delivery. Instead of waiting for manual system copies, large refresh cycles, and post copy clean up activities, SAP teams can now automate the movement of the right data into the right environment at the right time. When this process includes data masking, data subsetting, and automated patching, the result is faster refresh readiness, reduced privacy risk, smaller target systems, and much more efficient SAP Test Data Management. Faster delivery Automate data provisioning so environments are ready sooner without waiting for full system copy cycles. Smaller targets Use data subsetting to reduce volume and deliver only the business data required for the scenario. Safer data Apply data masking during provisioning so sensitive information is anonymised before it reaches non production. What this solves technically Automated provisioning reduces dependency on full refreshes, supports selective updates, enables controlled masking, and keeps SAP data usable for testing while lowering operational effort. Automated provisioning Data masking Data subsetting Object patching Explore Dynamic Data Replicator Talk to Our Team Automated Data Provisioning in SAP Deliver Masked, Subsetted, and Ready to Use Data Faster STEP 1 Provision Select the SAP business scope required for the test or training scenario. STEP 2 Mask Apply masking rules to HR, customer, vendor, and financial records. STEP 3 Subset Reduce volume by moving only the data needed for the business use case. STEP 4 Patch Refresh selected objects without a full system refresh. Automated provisioning delivers secure, smaller, and faster SAP test data environments Built for SAP Test Data Management, selective refresh, patching, masking, and subsetting Automated Data Provisioning in SAP combines provisioning, masking, subsetting, and patching to deliver usable and protected non production data faster. Automated Data Provisioning in SAP is no longer just about copying large volumes of data from one system to another. Modern SAP teams need a faster and more controlled way to prepare development, QA, training, and sandbox environments without relying on full system refreshes. When provisioning is automated, business relevant data can be delivered with less delay, less manual effort, and less unnecessary volume. When that process also includes masking, subsetting, and patching, the quality and usability of the resulting environment improve significantly. Why Traditional SAP Data Provisioning Slows Delivery Traditional SAP data provisioning is often based on full system copies or large refresh activities. While these approaches deliver complete data, they are usually slow, heavy, and inefficient. They move everything, including data that adds no value to the target scenario. This increases system size, extends refresh duration, and creates unnecessary operational work before the environment is usable. It also introduces a major security and privacy issue. Sensitive HR, customer, vendor, and financial data is frequently copied into non production systems that do not need to hold raw live values. long refresh windows delay projects and releases large data volumes increase target system footprint manual post copy clean up slows test readiness sensitive data is exposed in non production teams cannot easily provision scenario specific data The more data you move than you actually need, the slower, larger, and riskier the SAP provisioning process becomes. What Automated Data Provisioning in SAP Changes Automated Data Provisioning in SAP changes the model from bulk movement to controlled delivery. Instead of copying complete clients or full productive datasets, organisations can define the data they need and automate how it is prepared for the target system. This approach allows teams to provision environments with data that is: relevant to the specific test or business process masked where sensitive data exists subsetted to reduce size and overhead patched or refreshed selectively without full re-copy The result is faster environment readiness, lower database growth, and greater control over how SAP test data is managed across the landscape. Data Masking Built Into Provisioning One of the strongest benefits of automation is the ability to apply data masking during the provisioning process itself. This means sensitive values are transformed before they reach the non production environment rather than being copied raw and cleaned later. For example, employee personal details can be anonymised, customer email addresses can be converted to safe values, and financial records can be scrambled while retaining technical structure. What masking protects HR names, dates of birth, salary values customer identities and contact information vendor and business partner details financial and banking information Why built in masking matters reduces privacy exposure immediately avoids post refresh clean up effort keeps target systems safer by design supports realistic but protected data use Data Subsetting for Faster and Leaner SAP Systems Data subsetting is essential to modern SAP provisioning because not every use case requires a full production sized dataset. In many cases, teams need only a portion of the business scope. By moving just the relevant data, organisations reduce load size, improve refresh speed, and lower storage demand in the target system. This is especially valuable in S/4HANA programmes and in non production landscapes where database growth and performance have a direct operational cost. reduce unnecessary volume in target systems accelerate data provisioning cycles deliver smaller, more focused environments support use case based testing and training Automated Patching and Selective Refresh Full refreshes are not always necessary. In many situations, SAP teams only need to update a selected dataset or a defined business object. Automated patching supports this model by refreshing parts of the environment without disrupting the entire target system. This is a major advantage for continuous testing, agile delivery, and support landscapes where frequent selective updates are more useful than repeated full copies. patch specific business objects instead of everything refresh the required scope with less disruption improve responsiveness for project teams support repeatable object level updates Where automated provisioning creates value The value comes from speed, control, security, and reduced data volume. The business case
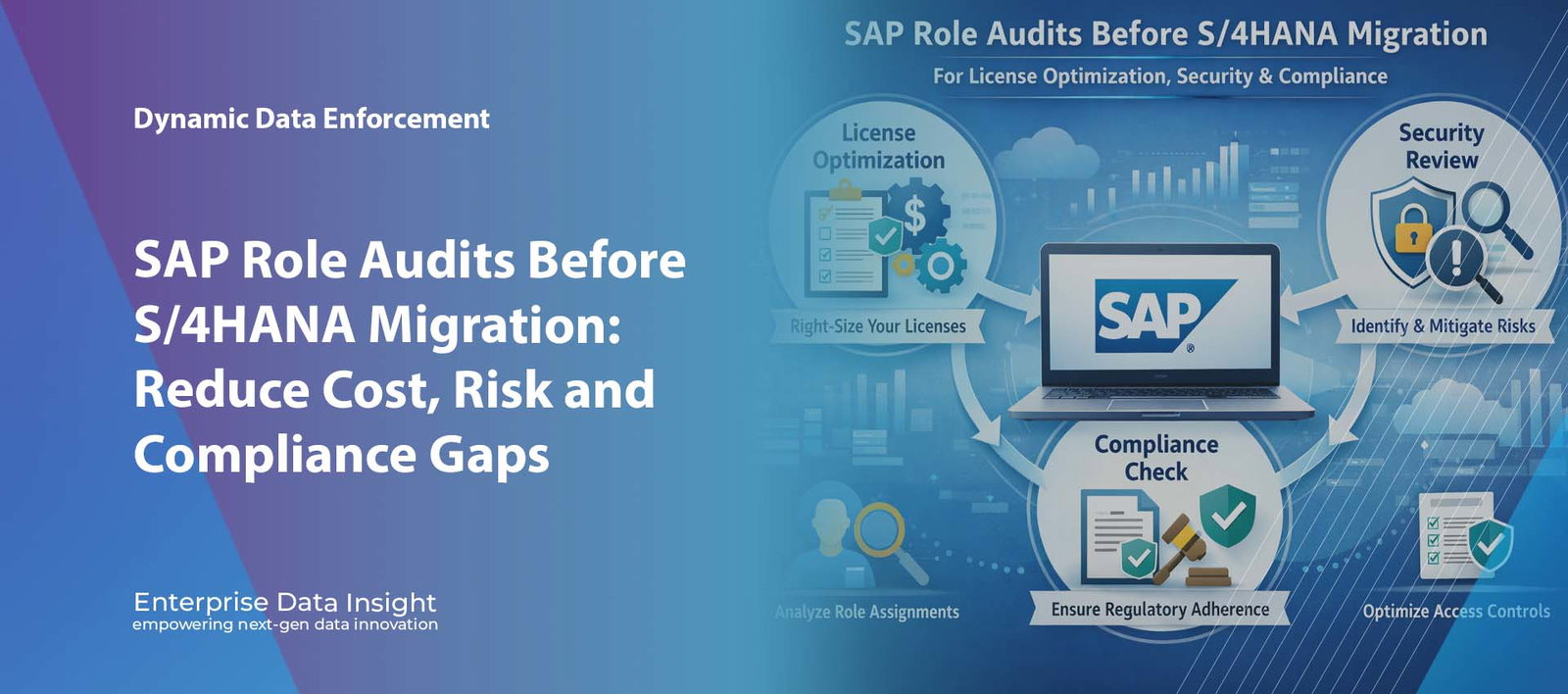
SAP GRC | SAP Security | S/4HANA Migration | Role Management Powerful SAP Role Audits Before S/4HANA Migration to Cut Cost, Strengthen Security and Improve Compliance SAP role audits before S/4HANA migration can uncover hidden licence waste, excessive access, weak Segregation of Duties control, and outdated authorisations before they are carried into the new platform. For organisations moving from ECC to S/4HANA, this workstream is not just a technical review. It is a business decision that improves cost control, protects sensitive data, and helps create a cleaner access model for the future environment. Lower spend Identify dormant users, duplicate accounts, and poor licence classification before migration. Stronger control Reduce broad access to payroll, finance, procurement, vendor, and customer records. Cleaner future state Improve role design and resolve SoD issues before S/4HANA goes live. How Enterprise Data Insight helps Enterprise Data Insight helps organisations analyse users, roles, authorisations, licence usage, and SoD exposure so the move to S/4HANA starts with better visibility and stronger governance. Role analysis Licence visibility Access simulation SoD governance Explore EDI GRC Solutions Talk to Our Team A role audit before migration helps reduce licence waste, tighten access, and improve governance before S/4HANA go live. Table of Contents Why role reviews matter before S/4HANA How an audit reduces licence waste How it strengthens security How it improves SoD compliance A practical SAP example How Enterprise Data Insight helps FAQ Conclusion Organisations preparing for S/4HANA often focus on data transformation, infrastructure, testing, and custom code. Yet many programmes leave one of the biggest risks untouched: the existing role model. Old roles, inactive accounts, duplicate identities, and broad access rights can all move into the target system unless they are reviewed early. Why SAP Role Audits Before S/4HANA Migration Matter A structured review of roles and authorisations gives businesses a clearer picture of who has access, why that access exists, and whether it still reflects real job responsibility. This matters because most SAP environments have evolved over many years, often through urgent changes, copied roles, manual workarounds, and limited clean up. Over time, organisations often accumulate: inactive and dormant users duplicate identities across SAP systems excessive authorisations roles that no longer match real responsibilities hidden SoD conflicts avoidable licence cost Reviewing access before S/4HANA helps prevent historical control issues from becoming future operational problems. How SAP Role Audits Before S/4HANA Migration Optimise Licence Spend One of the strongest business reasons for this activity is licence optimisation. Many organisations pay for more than they need because they cannot clearly see how users behave, which licence types are assigned, or whether access levels truly match real usage. A review can reveal where cost is being driven by poor classification, unused accounts, or duplicated access across different SAP environments. Combine users across systems In many landscapes, one person appears in several SAP applications with overlapping access and inconsistent licence treatment. Rationalising those identities can improve utilisation and reduce waste. Remove inactive access Some users log in rarely but still consume expensive licence categories. Identifying and removing dormant access frees capacity for real business demand. Better user classification also helps businesses avoid assigning higher cost licence categories where they are not justified by actual activity. Where savings usually come from Identify Find dormant users and redundant access still consuming cost. Classify Match users to the right licence category based on real behaviour. Consolidate Reduce duplicated identities across connected SAP systems. Reallocate Free up licence capacity without avoidable extra spend. How SAP Role Audits Before S/4HANA Migration Strengthen Security S/4HANA introduces broader ways to interact with enterprise data through Fiori, analytics, mobile usage, and connected business processes. That makes accurate access design more important than ever. A strong review helps organisations understand: who can access sensitive business data which roles expose payroll, finance, vendor, or customer records which users can change or extract critical information where broad access no longer matches business need how different personas should see different data This is especially relevant in HR, finance, procurement, master data, and business partner management where the impact of poor access design can be significant. Dynamic access questions where is the user coming from what data are they trying to access what device are they using what data are they trying to extract Data areas most exposed employee payroll data financial postings and journals vendor and supplier records customer and business partner data How SAP Role Audits Before S/4HANA Migration Improve SoD Compliance Segregation of Duties remains one of the most common control issues in SAP landscapes. A pre migration audit helps identify high risk combinations before they are moved into the future system. Common examples include: creating vendors and approving payments maintaining master data and posting transactions creating purchase orders and approving goods receipts posting journals and approving adjustments The best time to reduce SoD risk is before migration, not after go live when those conflicts are already embedded in the new environment. A Practical SAP Example Imagine an ECC system where a broad HR role has evolved over many years. General administrators, payroll specialists, and support staff all inherit similar permissions. During the review, the business discovers that some users can view salary data and deductions even though they only need employee master record access. If that role moves unchanged into S/4HANA, the same issue continues. A proper audit allows the organisation to separate responsibilities, redesign access by persona, and reduce exposure before migration. The real goal is not simply to review access. It is to build a cleaner, safer, and more efficient role model for the future SAP environment. How Enterprise Data Insight Helps Enterprise Data Insight helps organisations turn role audits into a structured and measurable migration workstream. Instead of relying on manual spreadsheets and fragmented review methods, teams gain better visibility across roles, users, authorisations, licence exposure, and SoD risk. Enterprise Data Insight supports: role and user analysis across SAP environments licence visibility and more accurate user classification access simulation for what if analysis SoD risk identification and governance
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…
The basic premise of search engine reputation management is to use the following three strategies to accomplish the goal of creating a completely positive first page of search engine results for a specific term…