SAP Access Control: Unlock Smarter Security with Attribute-Based Access (ABAC)

SAP Access Control With ABAC: Unlock Smarter Security With Dynamic Data Enforcement
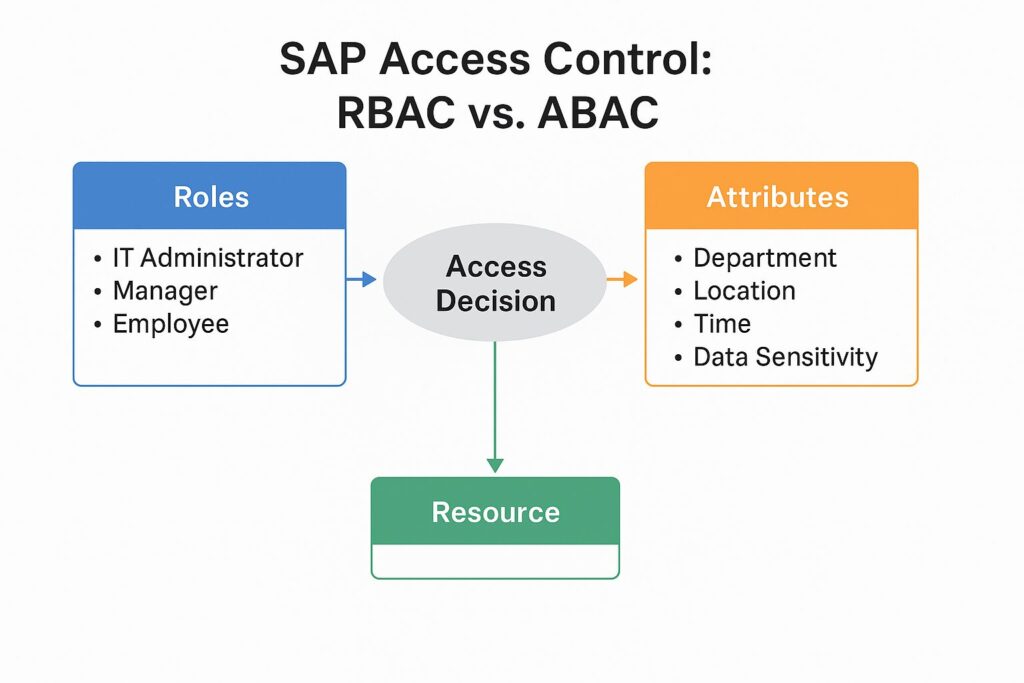
SAP access control becomes mission critical as your digital footprint grows. Relying on static roles alone can leave you exposed, especially when you are managing segregation of duties, remote access, and exception heavy workflows. The good news is you do not have to choose between flexibility and security. By complementing traditional role based access control with Attribute Based Access Control, ABAC, you can prevent violations in real time, not after the fact.
Introduction
As your company’s digital footprint grows, effective access control becomes mission critical. Relying on static roles alone leaves your system vulnerable, especially when you are managing segregation of duties, remote access, and exception heavy workflows.
By complementing traditional SAP Role Based Access Control, RBAC, with Attribute Based Access Control, ABAC, you can move from reactive controls to proactive prevention.
Understanding SAP access control using roles
In SAP, roles define what users can see and do. Functionally, they are collections of permissions that align access to job responsibilities and enforce the principle of need to know.
- Role assignment: only authorised users are granted access.
- Role authorisation: permissions are explicitly tied to those roles.
- Transaction authorisation: users can only perform approved transactions within their assigned roles.
Over time, SAP evolved RBAC to include hierarchies. Executives might inherit access from department heads and team leaders. While efficient, this model lacks the granularity needed for dynamic, exception heavy operations.
Why RBAC alone is not enough in modern SAP landscapes
RBAC was built for static, on premises environments, not today’s cloud first, hybrid access ecosystems. It is binary. You either have access or you do not.
Employees work remotely, handle cross functional responsibilities, and often need exceptions to get work done. When segregation of duties conflicts arise, RBAC does not know why or how a role is being used, only that a transaction is allowed.
Enhancing SAP access control with ABAC
Attribute Based Access Control, ABAC, extends RBAC by introducing dynamic conditions into the access decision. Think of attributes as context.
Department, job level, citizenship, clearance.
Read, write, approve, transfer.
Transaction code, document type, classification.
Time of day, IP address, device, location.
Real world example: why ABAC matters
Let’s say an IT administrator has full access to modify the user database. In an RBAC model, that person can do so anytime, from anywhere.
If the administrator is working remotely, they can only read the database. If they log in between 08:00 and 10:00 on weekdays, they can edit user data, and only within HR related tables.
This creates intelligent, time and context bound access, reducing risk without impeding productivity.
Hybrid SAP access control: RBAC + ABAC
The future of SAP security lies in layered access control. RBAC remains the foundation, defining the what. ABAC defines the how, when, and under what conditions.
- Fine grained control over sensitive operations.
- Dynamic SoD enforcement based on actual business context.
- Reduced false positives in GRC and audit reports.
- Greater agility for exception handling.
- Real time risk mitigation without user friction.
The cost of not adopting ABAC in SAP
Without ABAC, companies resort to creating excessive custom roles for each exception, over granting access and hoping logs will catch misuse, and spending hours manually reviewing SoD violations. This is not scalable. It is not secure. And it does not meet modern compliance standards.
Enterprise Data Insight: powering dynamic SAP access control
Enterprise Data Insight enables dynamic, real time access enforcement with Dynamic Data Enforcement, DDE. Built to work natively with SAP ECC and S 4HANA, DDE evaluates user, document, and environment attributes on the fly, blocks risky transactions before they happen, and logs every access decision for audit transparency.
Block risky actions before they complete.
Context driven control without rearchitecting.
Log who, what, when, where, and why.
Prevent violations dynamically, not retrospectively.
Conclusion: secure more, grant smarter
SAP access control is no longer just about granting roles. It is about making smart, real time decisions that adapt to your business context. With ABAC, you are not just controlling access, you are controlling risk.